quantum telecommunication encryption

- Background
1.1 Purpose
In order to simulate a complete quantum key distribution experiment, intuitively understand the implementation process of the classical BB84 protocol used in quantum key distribution, and use the distributed key for data encryption as communication. Additionally, depending on the requirements, modules such as EVE attack, decoy state, and single-photon detector can be added.
1.2 Quantum Theory
A quantum is the smallest indivisible fundamental unit in the field of physics. For example, the smallest unit of light is the photon, also known as a 'quantum of light,' which is a type of quantum.
In quantum communication, information is transmitted using the polarization states of photons (it can also be the phase or spatial information of photons).
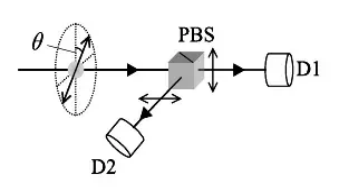
Figure 1-1
Taking polarization states as an example, a single photon is modulated to a specified polarization angle, and at the receiving end, a polarizing beam splitter directs the photon to either single-photon detector D1 or D2.
The probability of D1 detecting a single photon is cos2θ, the probability of D2 detecting a single photon is sin2θ。
1.3 Protocol Overview
The BB84 protocol is a QKD protocol proposed in 1984 by Charles H. Bennett and Gilles Brassard, and it is also the first QKD protocol. In the BB84 protocol, the sender randomly sends single photons under two sets of non-orthogonal basis vectors, and the receiver randomly chooses basis vectors for measurement. Ideally, when both use the same basis vectors, the two parties will obtain a secure and consistent key. The BB84 protocol requires encoding with two sets of non-orthogonal basis vectors. In polarization encoding, one can choose the horizontal-vertical basis (commonly denoted as the Z basis), which includes the two polarization states |H> and |V>, and the diagonal basis (commonly denoted as the X basis), which includes the two polarization states |±> = (|H> ± |V>)/2, generally also called the |+> and |-> polarizations. These four states are commonly referred to as BB84 states.
The basic operation process of the BB84 protocol is as follows: Alice randomly selects one of the four BB84 states to prepare a single-photon quantum state and then sends it to Bob through a quantum channel. Upon receiving the quantum state sent by Alice, Bob randomly chooses either the Z or X basis for measurement and records the measurement result. Subsequently, Alice and Bob compare their encoding bases and measurement bases through a public authenticated channel, retaining the coding bits and measurement results corresponding to the same bases, thereby obtaining a string of raw keys.
Alice and Bob can estimate the error rate by randomly revealing and sampling some of the bits. If the error rate exceeds a certain theoretical threshold, the raw key is discarded and the process is repeated; otherwise, a secure key is obtained through data post-processing procedures such as error correction and privacy amplification. Error correction can correct the raw key containing errors into an identical key string, while privacy amplification reduces the information available to Eve about the key by compressing its length to a sufficiently small amount.
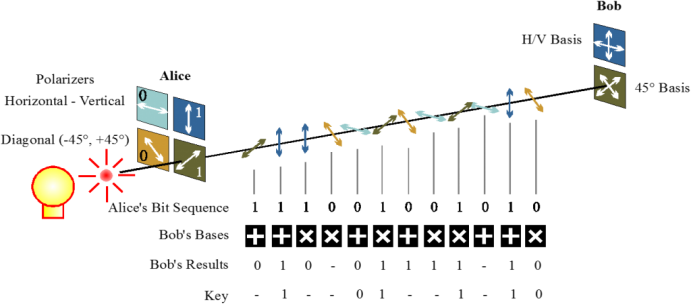
Figure 1-2
2.Product Introduction
2.1 Product Composition
The system product consists of a transmitter, a receiver, and the corresponding software.

Figure 2-1 Overall Appearance of the Alice Transmitter

Figure 2-2 Front View of the Alice Transmitter

Figure 2-3 Overall Appearance of the Bob Receiver

Figure 2-4 Main View of Bob Receiver
2.2 Core Features
- Demonstrate the process of learning quantum key distribution using classical methods, making it more general and accessible.
- Using data generated by hardware directly for the basis comparison process in the BB84 protocol is closer to practical implementation.
- Demonstrate the data post-processing procedures, understanding the entire process of error correction and privacy amplification.
- It can achieve a continuous quantum key generation process.
- Applying the generated key in practical communication processes provides a deeper understanding of the role of quantum key distribution.
2.3 Main Functions
- Polarization Preparation and Detection Experiment
- Data Post-Processing Experiment
- Key Distribution Experiment
- Encryption and Decryption Experiment
2.4 Technical Specifications
| Parameter Name | Indicator | Unit | Remarks |
| Encoding Method | Polarization Coding | ||
| Wavelength | 1550 | nm | |
| Operating Frequency | 100 | kHz | |
| Detection Efficiency | 10~30 | % | Adjustable |
| Bit Error Rate | <3% | ||
| Optical Interface | FC/PC | ||
| electricity supply | 12V Adapter | Less than 5A |
2.5 Device Connection
The computers consist of two all-in-one machines. During normal experiments, it is necessary to properly connect the power supply, and both ends should be connected synchronously using a single SMA cable. Single-mode optical fiber is selected for the connection, and attention must be paid to the cleanliness of the optical fiber and the correct installation of the flange during the connection.
The network is entirely connected using Ethernet cables, generally required for connections between devices to enable data exchange between both ends. Connections between computers and devices are made to facilitate the issuance of commands, the uploading of status information, and the exchange of raw data.
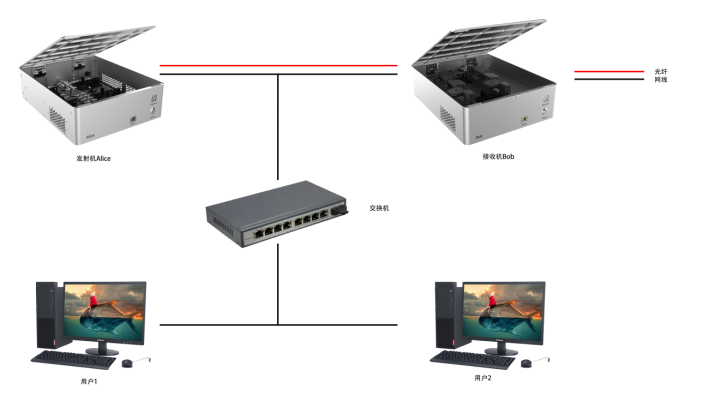
Figure
2-5 Device Connection Diagram
quantum research(other experimental studies))

